INCIDENT RESPONSE AND
In under 1 day after our scanner runs, you will receive a fully actionable report, explained to you step-by-step by our CyCraft Incident Response (IR) & Fast Forensic Services team. We’ve assisted dozens of international organizations in investigating critical security incidents, conducting thorough digital forensic analyses, and accelerating maturity in long-term security solutions.
Is your network air-gapped or segmented? Not a problem.
CyCraft IR & Fast Forensic Services can run investigations on-site and guarantees data privacy and zero data leakage. Your sensitive data never goes to the cloud.
WE
ADDRESS
YOUR
DEEPEST
CONCERNS
- How did they first break in?
- Is there malware?
- What did it do?
- How do I stop C2 communications?
- How do I clean my user accounts?
- What data was affected? Stolen?
- How do I get everything back to good?
- How do I remove hacker tools?
- How can I prevent intrusions in the future?
- How can I do all of the above fast, accurately, simply, and thoroughly?
WE ADDRESS YOUR THREATS
Today, organizations face a myriad of threats, from script kiddies to state-sponsored advanced persistent threats. CyCraft IR & Fast Forensic Services are here to help you detect, contain, and eradicate them.

FINANCIAL
Threat groups target not just your business’ financials but also your customers’. This includes payment card data theft and ransomware.

INTELLECTUAL PROPERTY THEFT
Sophisticated state-sponsored attacks are known to target trade secrets, proprietary product IP, and other sensitive information.
SUPPLY CHAIN ATTACKS
Threat groups target less secure elements in your supply chain to infiltrate your environment and exfiltrate or destroy sensitive data.

SPEAR PHISHING
Socially-engineered attacks effectively target your staff. While typically emails and texts, this now includes voice/audio deepfakes, with video deepfakes now on the horizon.

RANSOMWARE
Attackers can copy, exfiltrate, and delete your sensitive data in seconds. Ransomware attacks are rapidly increasing in frequency, severity, and complexity.
INSIDER THREATS
Insider threats can instantly bypass layers of security and are launched by people within your organization, former employees, contractors, partners, or business associates.
WE PROVIDE YOUR SOLUTION
Our expert team of analysts leverages automated digital forensic analyses to provide you with an immediate detailed analysis of your cyber situation. We work with you to contain threats, minimize their impact, and get your business back to healthy in 4 fast steps.

FAST
Under 1 day after our scanner runs, you receive an eradication plan with complete site-wide hacker tools and behavior analysis, provided by the seamless collaboration between our expert analysts, our virtual forensic analyst AI & attacker-behavior modeling technology.
ACCURATE
We provide automated forensic analysis not just across multiple levels of context but also into the intricate relationships between each of those levels of context.
SIMPLE
Our CyCraft IR Services Team takes you through your fully-actionable eradication plan, explaining each step simply and clearly.
THOROUGH
We re-scan and confirm eradication with cyber threat intelligence from multiple major proprietary sources and organizations across the globe, as well as the rigorous AI-driven vetting process of CyberTotal.
THE NEED FOR INCIDENT RESPONSE
SOCs, CSOs, and CISOs aren’t judged by their everyday routine but on their response to their worst day–a security breach. Incident Response investigations combat and manage the aftermath of a security breach. You need to reduce your mean-time-to-detect (MTTD) and mean-time-to-respond (MTTR) to ensure you get out of the nightmare while limiting damage to your system and your data.
CyCraft IR & Fast Forensic Services provides automated IR investigation, allowing our customers a F/A/S/T recovery so that they can get back to business faster and more secure.
THE NEED FOR
INCIDENT RESPONSE
SOCs, CSOs, and CISOs aren’t judged by their everyday routine but on their response to their worst day–a security breach. Incident Response investigations combat and manage the aftermath of a security breach. You need to reduce your mean-time-to-detect (MTTD) and mean-time-to-respond (MTTR) to ensure you get out of the nightmare while limiting damage to your system and your data.
CyCraft IR & Fast Forensic Services provides automated IR investigation, allowing our customers a F/A/S/T recovery so that they can get back to business faster and more secure.
OUR APPROACH
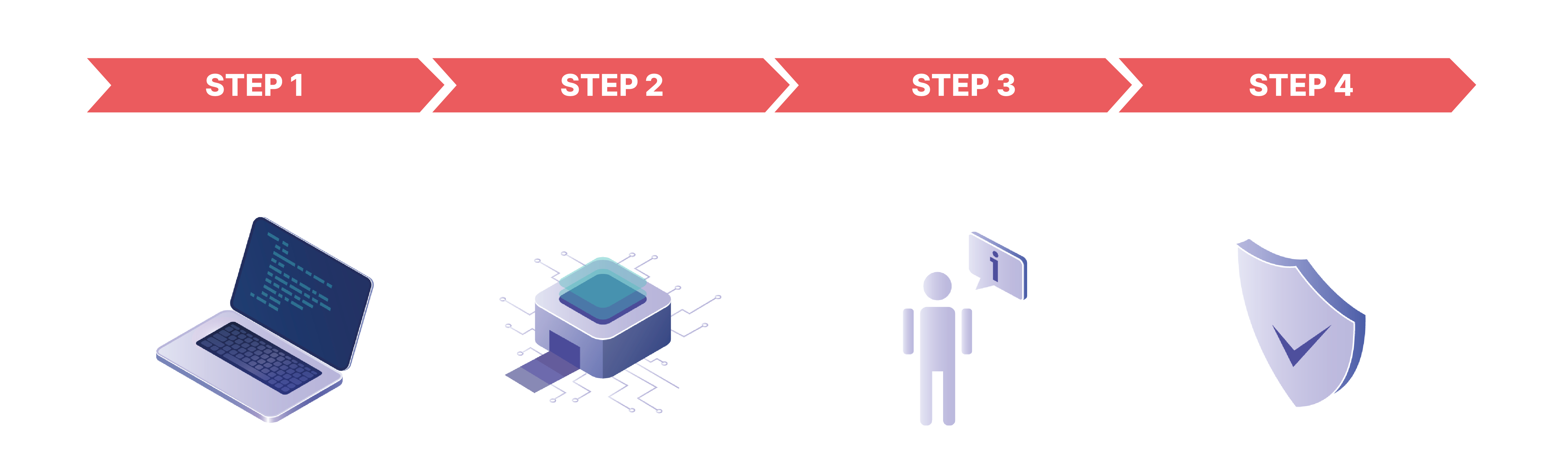
OUR APPROACH

Deploy our AI forensic scanner to your endpoints.


We receive the data and our AI experts analyse.

Based on the findings we develop and execute a plan.

Together we rescan to confirm eradication.

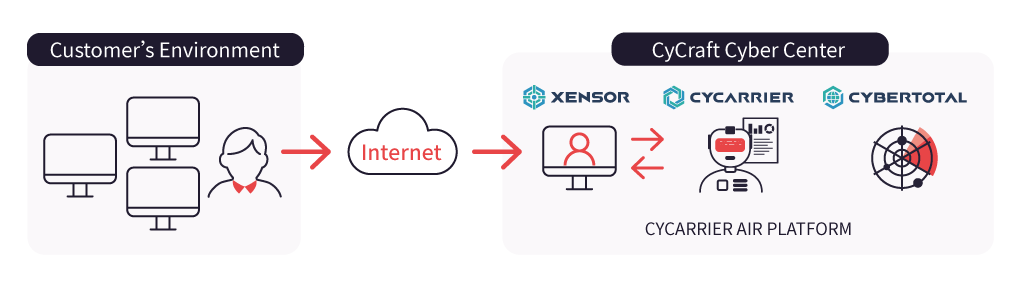
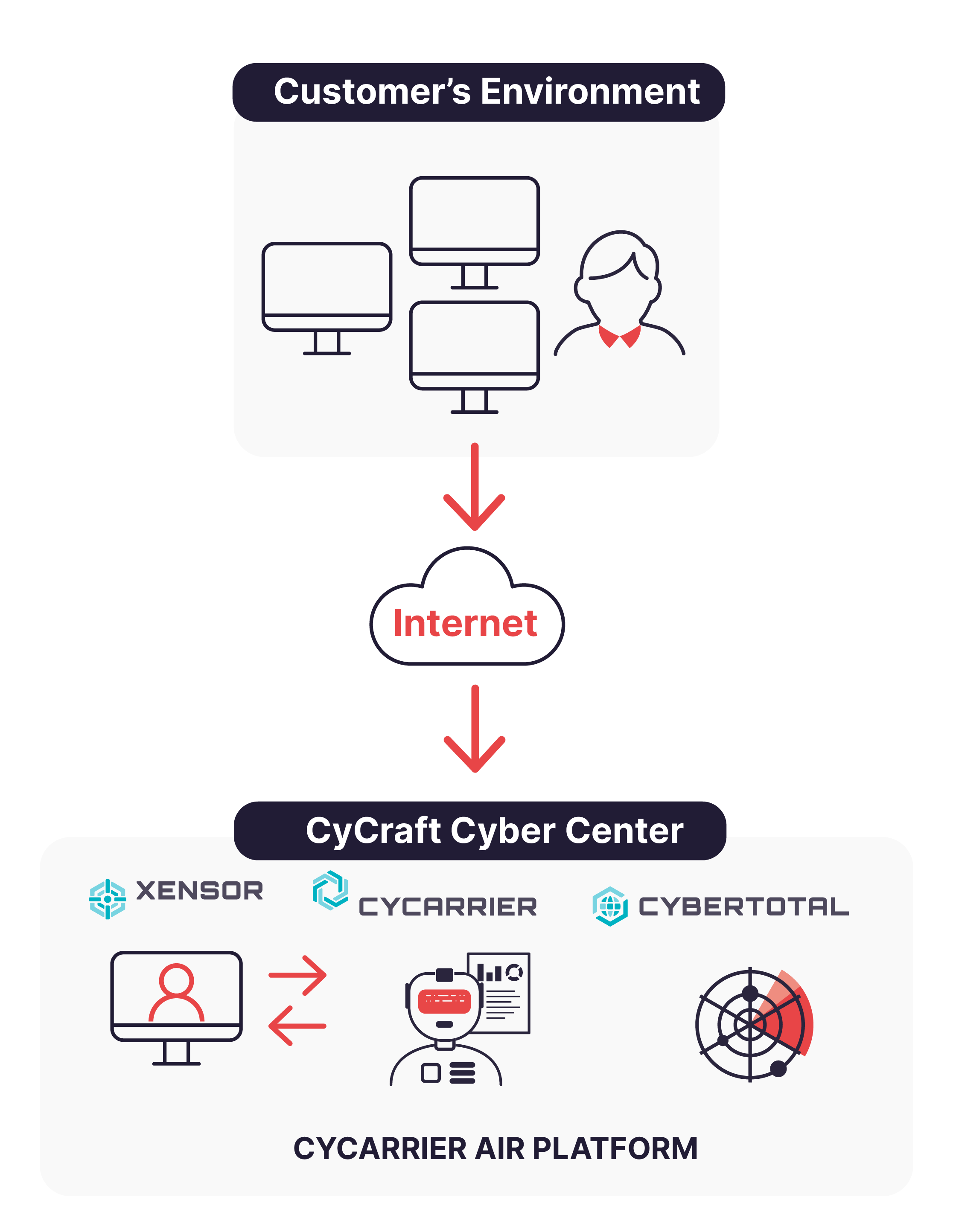
CLOUD ENVIRONMENT SETTINGS
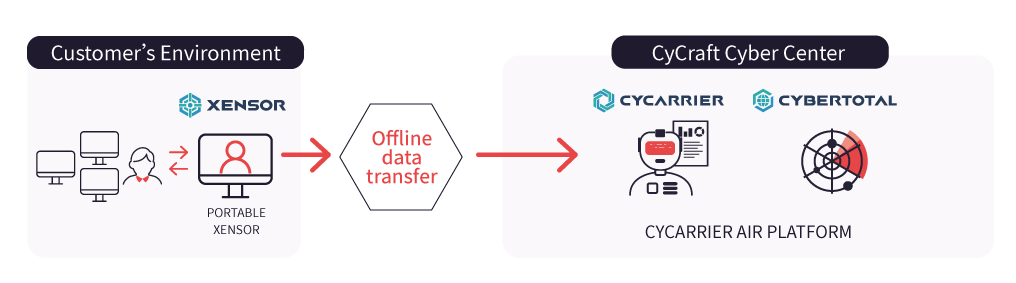
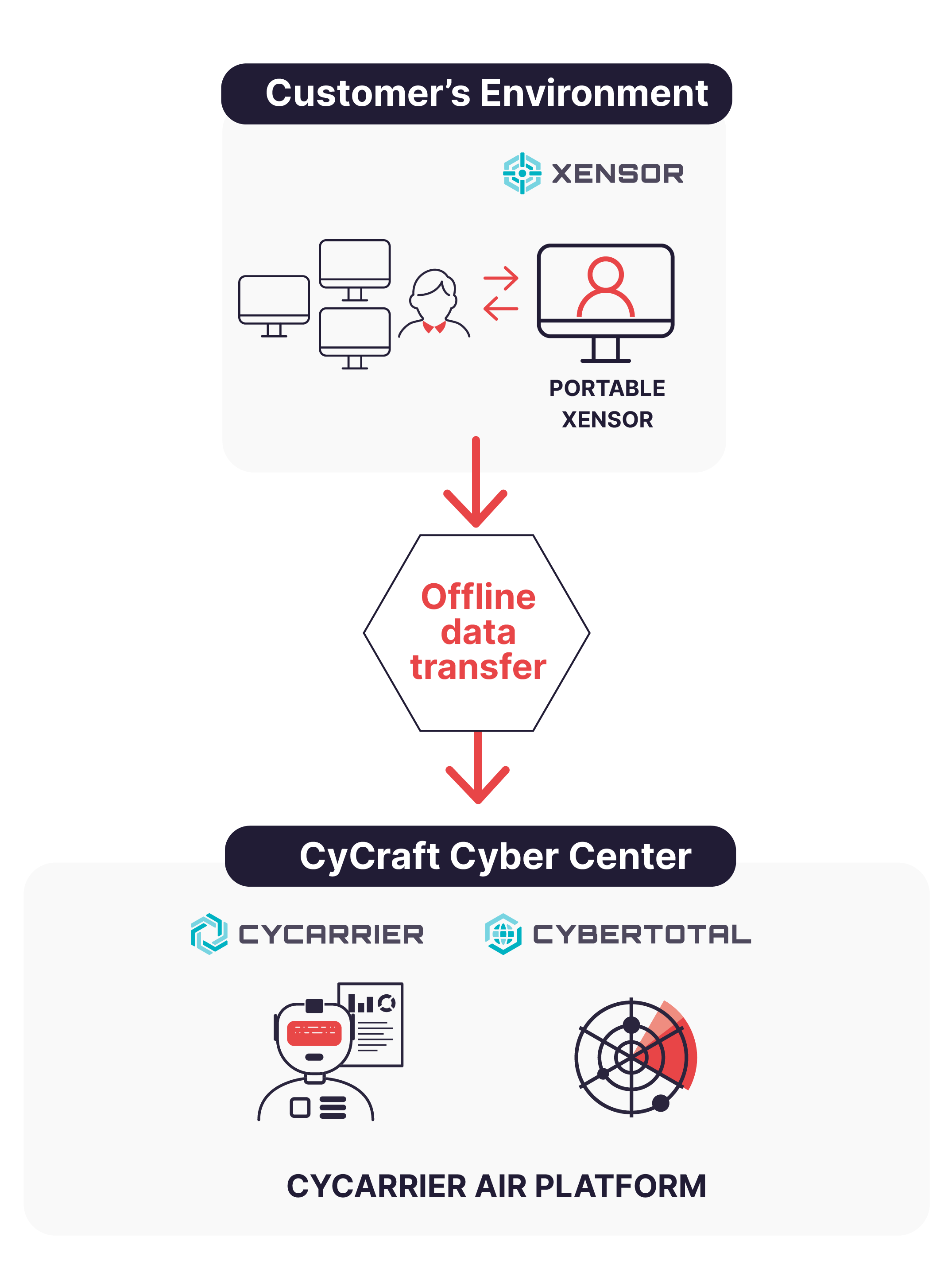
CLOSED ENVIRONMENT SETTINGS
CLOUD ENVIRONMENT SETTINGS
CLOSED ENVIRONMENT SETTINGS
WE’RE THOROUGH
CyCraft IR & Fast Forensic Services is the only IR service with the expertise and technology to leverage automated intelligent forensics to analyze security incidents across 7 levels of context to ensure your environment is thoroughly clean and back to healthy.
LEVEL 7
Virtual Forensic Analyst Context: CyCraft AIR, our AI-driven security platform, leverages AI-behavioral automation of investigative methods to combine all of the below levels into a final analysis, gaining you a full understanding of your cybersecurity situation.
LEVEL 6
Global Threat Intelligence Context: After thoroughly vetting global threat intel, CyCraft IR Services correlates it with behaviors and artifacts found at the lower levels.
LEVEL 5
Org-Wide Context: Link together evidence found across the lower levels of context and examine them in the context of the entire organization.
LEVEL4
User Context: Examine user behaviors, successful logins, and failed attempts, etc.
LEVEL 3
Isolated Artifact Context: a packet, an execution, a memory segment, or log file entry are among the many examples of isolated artifacts.
LEVEL 2
Network Context: Examine the connections between systems in terms of the various protocols and behavioral purposes of the connections
LEVEL 1
Endpoint Context: Forensically scan the endpoint event logs, memory, startup files, processes, and more.
WE’RE THOROUGH
CyCraft IR & Fast Forensic Services is the only IR service with the expertise and technology to leverage automated intelligent forensics to analyze security incidents across 7 levels of context to ensure your environment is thoroughly clean and back to healthy.
LEVEL 7
Virtual Forensic Analyst Context: CyCraft AIR, our AI-driven security platform, leverages AI-behavioral automation of investigative methods to combine all of the below levels into a final analysis, gaining you a full understanding of your cybersecurity situation.
LEVEL 6
Global Threat Intelligence Context: After thoroughly vetting global threat intel, CyCraft IR Services correlates it with behaviors and artifacts found at the lower levels.
LEVEL 5
Org-Wide Context: Link together evidence found across the lower levels of context and examine them in the context of the entire organization.
LEVEL4
User Context: Examine user behaviors, successful logins, and failed attempts, etc.
LEVEL 3
Isolated Artifact Context: a packet, an execution, a memory segment, or log file entry are among the many examples of isolated artifacts.
LEVEL 2
Network Context: Examine the connections between systems in terms of the various protocols and behavioral purposes of the connections
LEVEL 1
Endpoint Context: Forensically scan the endpoint event logs, memory, startup files, processes, and more.
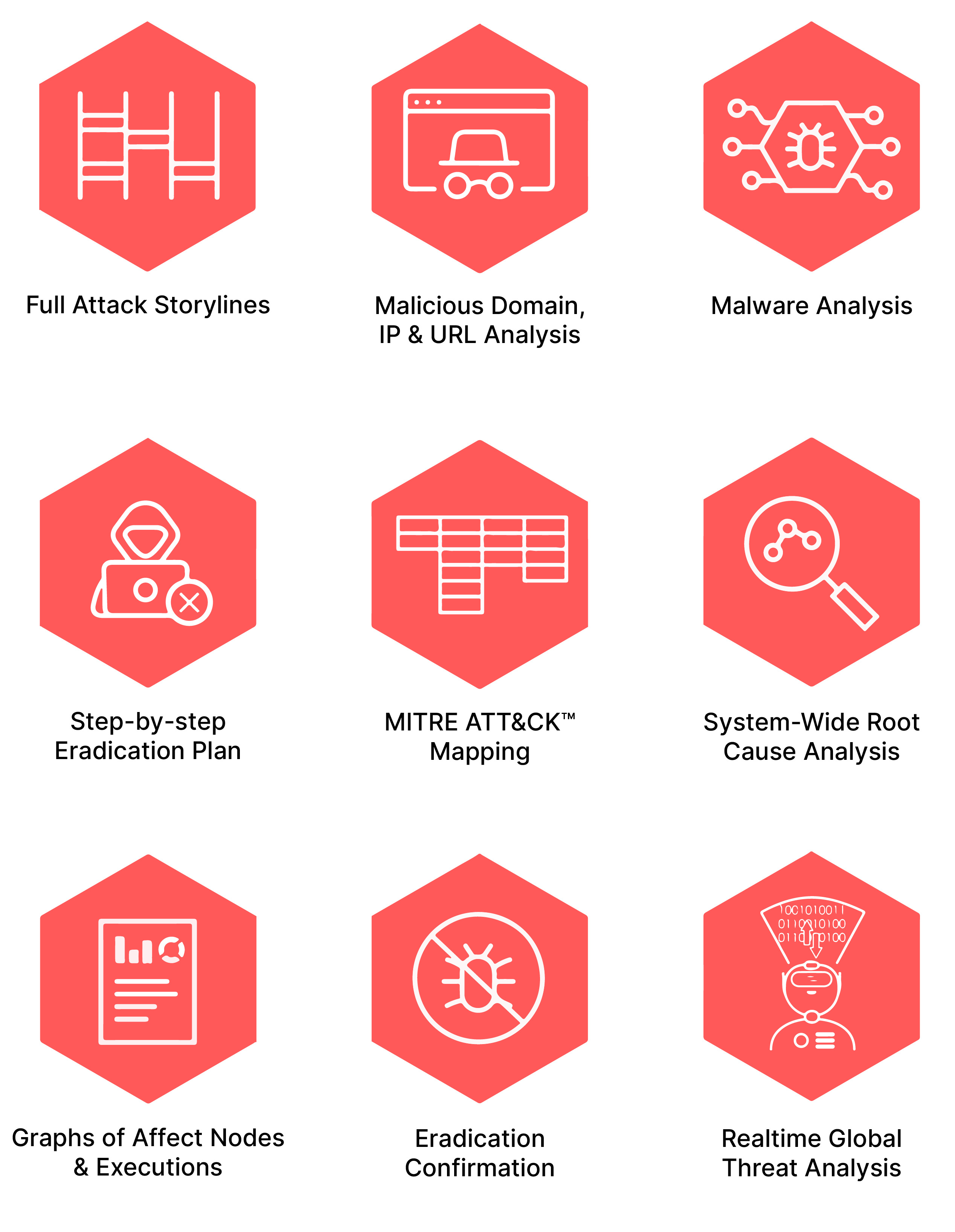
OUR DELIVERABLES
We provide you with clear, concise, and fully actionable reports covering
everything you need to know to get back to healthy stat.
Full storylines of any & all malicious activity

Malware analysis



Graphs of all affect nodes and executions

Up-to-date Global Cyber Threat Intelligence
OUR DELIVERABLES
We provide you with clear, concise, and fully actionable reports covering
everything you need to know to get back to healthy stat.
WHY CYCRAFT?
INDUSTRY RECOGNITION
In the past year, CyCraft outperformed all other MITRE ATT&CK® Evaluation vendors in Technique, Tactic, and General detections with zero configuration changes. CyCraft AIR and CyberTotal both received the Best of Show Grand Prize Award for Security Solutions at Interop Tokyo 2020; CyCraft also received 20+ 2020 Cybersecurity Excellence awards in categories including Managed Detection and Response, Incident Response, Threat Intelligence, and Artificial Intelligence. CyCraft is a proud member of FIRST, a premier organization for incident response security teams.





COMPETITIVE SOLUTIONS
MITRE ATT&CK Evaluations Validates Industry Leadership for CyCraft AIR Managed Detection and Response. CyCraft AIR scored more real-world GTT detections (General, Tactic, and Technique) than any other vendor solution and with zero configurations.
ANALYST RECOGNIZED
for intelligence-led Cybersecurity by leading global research firm IDC.

ISO 27001 CERTIFICATION
CyCraft is certified for ISO/IEC 27001:2013 certification, demonstrating CyCraft’s consistent commitment to thoroughly evaluating security risks, the design and implementation of controls, and the maintenance of effective processes to manage security. Everything Starts From Security
CYCRAFT
COMMUNITY TESTIMONIALS
“CyCraft has a deep understanding of information security and top-tier technology to prove it.”
Telecommunications, Japan
“CyCraft’s AI-driven managed detection and response, automated forensics, and security visualization showed us the key points and enterprise-wide root cause of all attacks, as well as greatly reduced our investigation time.”
Telecommunications, Taiwan
“CyCraft’s customer support provided excellent communication, incident reports, and response times, leaving us feeling confident and at ease with our security situation. “
Telecommunications, Taiwan
“We were impressed with their innovative technology, such as their intuitive dashboard that made it easy for analysts to analyze and re-analyze intrusion attack data.”
Interop Tokyo 2020, Best of Show Award’s Judge
PROUD TO PROTECT
TAIWAN CRITICAL
INFRASTRUCTURE
The CyCraft Community is our Priority.
Everything Starts From Security.





PROUD TO PROTECT
TAIWAN CRITICAL
INFRASTRUCTURE
The CyCraft Community is our Priority.
Everything Starts From Security.

CYCRAFT
IS TRUSTED BY
Fortune 500
Companies
Financial
Institutions
Law
Enforcement
Government
Agencies
Critical
Infrastructure
Airlines
Manufacturing
Hi-Tech
Telecoms
S0Cs
Many more…
CYCRAFT
IS TRUSTED BY

RELATED RESOURCES
ABOUT CYCRAFT
SERVICES
CyCraft Services provides organizations worldwide with the innovative AI-driven technology necessary to stop cyber threats in the 2020s. The CyCraft AIR platform is uniquely designed to detect the latest trends in malicious behavior, automate investigations, and auto-triage alerts, allowing CyCraft customers to detect, track, contain, and eradicate threats in real-time.
This unique approach empowers CyCraft customers to terminate unauthorized access to their environments faster and prevent intrusions from escalating into business-altering incidents. CyCraft also provides customers with proactive services to improve their visibility, elevate their threat intelligence on threats targeting their industry, hunt down threats, fill in defense gaps, and harden their defenses because everything starts from security.
F / A / S / T RESPONSE
FAST | ACCURATE | SIMPLE | THOROUGH
Your CyCraft representative is standing by to help you with an incident or answer any question regarding our incident response, compromise assessment, or managed detection and response services


